In this blog, we explain the purpose of ISO 27001 Clause 9.1 and why monitoring, measurement, analysis and evaluation are essential to demonstrating that an information security management system (ISMS) is operating effectively. We outline what organisations should monitor, how methods and responsibilities should be defined, and what criteria help determine acceptable performance. The blog also explores how results should be analysed, reported and used to drive continual improvement and maintain a robust, audit-ready ISMS.
Clause 9.1 (Monitoring, measurement, analysis and evaluation) of ISO 27001 requires organisations to determine what aspects of the ISMS need to be monitored and measured, how and when monitoring and measuring should be undertaken, when monitoring and measuring results will be analysed and evaluated, and who is responsible for performing these activities. The Clause further requires documentary evidence to be retained and the performance of the ISMS to be evaluated based on the results of the monitoring and measurement.
What Does Conformance to Clause 9.1 Involve?
Clause 9.1 identifies the areas you need to cover in developing your monitoring, measurement, analysis and evaluation approach, with this approach needing to be set out in framework and/or process documentation.
Define what needs to be monitored and measured
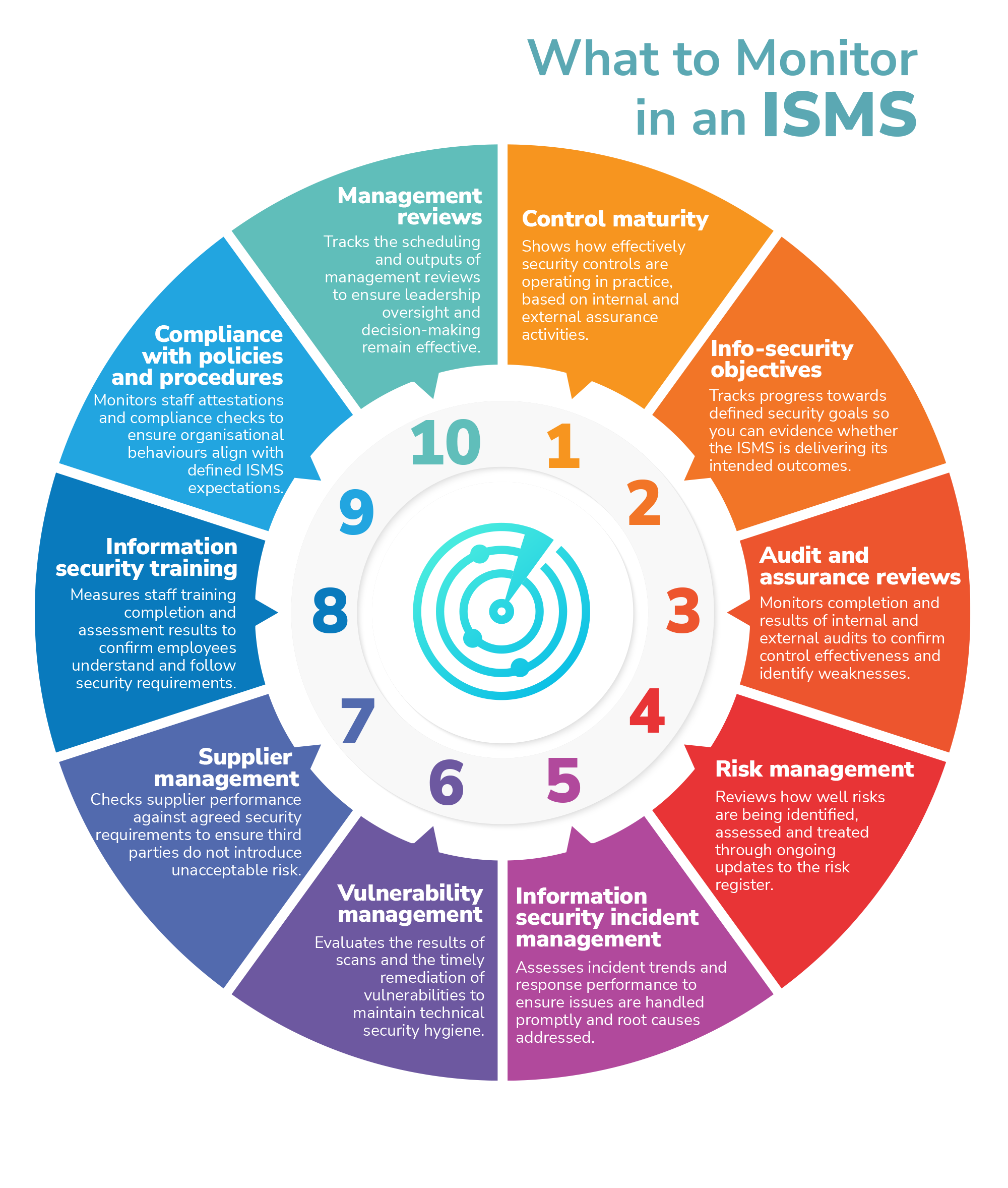
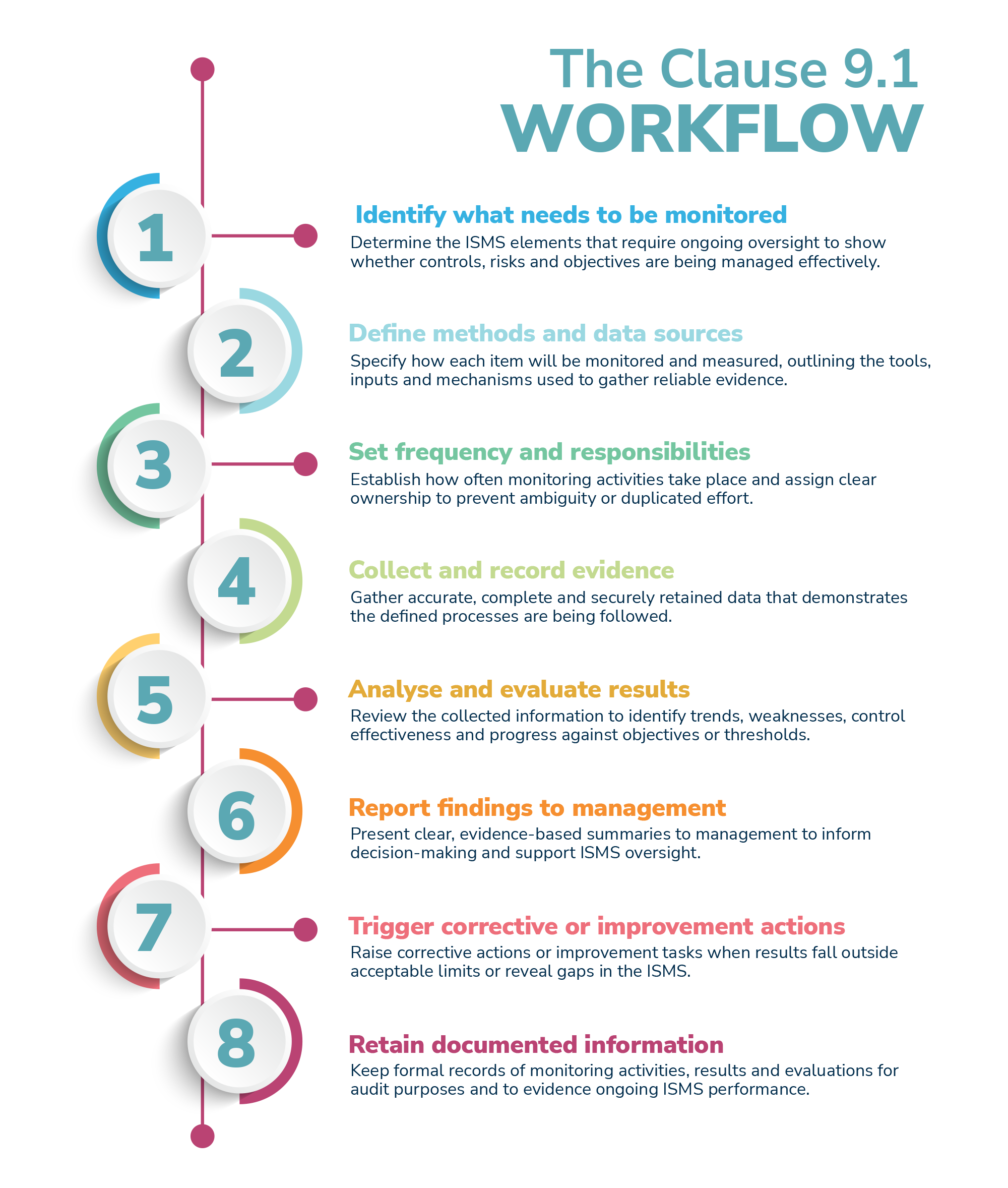
First, you will need to identify the ISMS elements that require ongoing oversight, which will form the basis of your ISMS performance measurement framework. Typical areas to be monitored can include, but are not limited to:
- Control maturity: an assessment of how well security controls are being performed, which can draw directly from internal and external audit results
- Information security objectives: progress towards achievement of information security objectives, which can either be long-standing objectives or those defined on a year-to-year basis
- Audit and assurance reviews: delivery and results of internal and external audits
- Risk management: performance of ongoing risk management activities, for example the regular review of open and accepted risks
- Information security incident management: incident trends and response times
- Vulnerability management: performance of regular vulnerability scans and treatment of identified vulnerabilities
- Supplier management: records of performance of suppliers against information security requirements
- Information security training: records of timely completion of information security training, indicative results of assessments included as part of the training and escalation of non-completion of training
- Compliance status: completion of planned compliance-related activities on time and as scheduled
- Management reviews: completion of ISMS management reviews on schedule and outputs from the reviews (note that monitoring and measurement can be an input to the management reviews, and subsequently draw on the outputs from management reviews to provide a feedback loop)
- Compliance with policies and procedures: records of employee attestations to comply with the information security policy and requirements of the ISMS.
Establish methods for monitoring and measurement
To ensure consistency and repeatability, you must define methods for the monitoring and measurement of each item (control maturity, training, objectives, etc.) identified in the previous step.
You will need to establish how the item will be monitored; depending on the item in question, this could be through the use of automated tools (for example reports generated from an incident management system), manual review of records (such as risk management reviews), audits (summaries of audit results), or some other mechanism.
In addition, you must determine how the item will be measured. This could include the use of key performance indicators (KPIs), such as completion of objectives against target dates, or thresholds to allow response to items that demand attention. For example, you may set a threshold of ‘no critical information security incidents in the quarter’, whereby the occurrence of any such incident would trigger a wider review of information security and the ISMS to determine how further events can be avoided. Scoring models, which are structured, numerical frameworks used to evaluate, rank, and prioritise options, may also be applied, although their complexity means they would only be recommended for the most mature ISMS’.
Finally, you need to define what data sources will be used, which could be as simple as audit reports to more complex data structures that allow for information extraction, such as a database of vulnerabilities identified, as well as defining what tools or systems support the process.
Define frequency and responsibilities for monitoring
Your organisation needs to clearly define when monitoring and measurement activities occur, and who is responsible for the activities, ensuring the frequencies and individuals you select are appropriate for the nature of that activity. You may, for example, decide to conduct daily log reviews (as part of incident management, perhaps), monthly KPI reporting, quarterly vulnerability scans or annual internal audits. Meanwhile, the ISMS Manager may be responsible for monitoring details of scheduled ISMS activities, the IT Security Team, CISO, etc., for vulnerability management-related monitoring and measurement, HR for training metrics and Procurement for details of supplier monitoring.
This information can be set out in a roles and responsibilities documents, or within process documentation. Regardless of where these details are documented, you must ensure all significant points are covered unambiguously (i.e., similar responsibilities are not allocated to multiple individuals, creating confusion over who should be doing what).
Document criteria for acceptable performance
To facilitate meaningful, consistent and repeatable performance evaluation, you need to define what ‘good’ ISMS performance looks like, including:
- Target values: the definition of what would be an acceptable result, for example that the expected completion rate for information security training is 100% of employees
- Tolerances: an acceptable variation from the ideal, expected result, such as 90% completion of information security training
- Thresholds and trigger points for corrective action: the point at which a result is no longer considered acceptable and should initiate further activity, such as raising a corrective action.
Collect and record data
Your organisation needs to be able to evidence that the processes it has defined have been implemented. The processes must therefore support the collection of evidence by gathering intelligence from relevant sources (e.g., system logs, management reports, audit results, vulnerability scans, training records, etc.), ensuring data gathered is accurate, complete, and retained securely, and using automated tools where possible to reduce the risk of errors.
Analyse and evaluate the results
The collection of information as set out above delivers little value if the results of the monitoring and measurement aren’t analysed and evaluated. As such, you need to establish how such analysis and evaluation will be undertaken, for example how you will:
- Identify trends, anomalies, and recurring issues
- Compare results against targets and thresholds
- Assess whether controls are effective
- Determine if risks are increasing or decreasing
- Evaluate whether information security objectives are being met.
The outcome of the analysis will feed directly into management reviews (Clause 9.3).
Report findings to management
As well as feeding results into management reviews, the most effective monitoring and measurement strategies feed results to executive management throughout the year to give them the insight they need to make operational decisions. This can be provided through regular ISMS oversight meetings (perhaps a quarterly security oversight committee), or through regular written reports. It is important to ensure that in all reports to executive management, summaries are clear, evidence-based, linked to risks and/or objectives and identify achievable actions.
Trigger corrective actions where needed
It is possible that monitoring and measurement will identify where the ISMS is not working correctly, or at the very least can be improved. After all, why undertake monitoring and measurement if it will not lead to improvements? Improvement opportunities need to be handled through established mechanisms for continuous improvement (Clause 10.1), whilst any issues identified that demonstrate a gap in the ISMS, or that the ISMS is not working correctly, need to result in nonconformities and corrective actions being raised (Clause 10.2). This could trigger updates to risk assessments, improvement of (or establishing new) controls, revision of processes, or perhaps adjustment of the ISMS objectives.
Maintain documented information
In addition to documenting the processes followed, setting out what is monitored and measured and how this is achieved, you must retain evidence of the monitoring and measurement’s results, and of the analysis and evaluation of the results. It is necessary to retain this evidence for an absolute minimum of 12 months for use in external assessments and, ideally, for at least the three-year certification period.
Build monitoring and measurement into the ISMS design
The approach for monitoring and measuring needs to be built into the ISMS in the early stages of its development. As part of a Stage 1 ISO 27001 audit, an external assessor will expect to see these processes in place, whereas by Stage 2 the assessor will expect to see evidence that the required information is being gathered. Failure to define the approach ahead of a Stage 1 assessment is likely to prevent certification progressing.
Why Does Monitoring, Measurement, Analysis and Evaluation Matter?
Information security management must be compatible with your organisation’s business objectives and processes for it to work in practice. While leadership support is necessary to achieve this, it is equally necessary to monitor how well an ISMS is performing and feed that information back to the individuals sponsoring information security within the organisation (i.e., to management). Monitoring ISMS performance is a key tool for management to ensure information security is being managed consistently and appropriately, and in turn maintain ISO 27001 certification. It is also central to the ISMS’ continual improvement, a concept at the heart of the Standard. Ultimately, effective implementation of Clause 9.1 ensures that your organisation is able to demonstrate ISMS effectiveness, find and remediate gaps before they widen into major nonconformities, identify improvement opportunities, and maintain a security posture that evolves in line with your risks and objectives.
How URM Can Help
Leveraging 2 decades of experience assisting organisations’ ISO 27001 implementation, URM is the ideal partner to support any aspect of your organisation’s conformance to the Standard.
Our large team of consultants can offer a range of ISO 27001 consultancy services to help you meet the Standard’s requirements; for example, we can conduct an ISO 27001 gap analysis where we establish your current level of conformance, and help you conduct your risk assessment using our proven risk assessment tool, Abriska 27001. Following this, we can work with you to develop policies, processes and ISMS infrastructure, always ensuring that these are both aligned with the Standard’s requirements and your organisation’s unique needs. URM can also offer a range of ISO 27001 internal audit services, including conducting an internal audit ahead of your certification assessment to ensure you are conformant, planning and implementing a full 3-year audit programme, or auditing more specific ISMS areas or particular controls.
As well as consultancy services, URM regularly delivers ISO 27001-related training courses. Our Introduction to ISO 27001 Course explores all aspects of information security and the importance of ISO 27001 in protecting information, whilst our Certificate in Information Security Management Principles (CISMP) Training Course will fully prepare you to sit and pass the BCS-invigilated examination and gain an industry-recognised information security qualification.
A short, free, non‑commitment call can help you clarify scope, understand regulatory expectations, and align your approach across standards such as ISO 42001 and NIST AI RMF. Early guidance often saves time and avoids fragmented compliance efforts.
Whether you are at an early planning stage or preparing for audit and assurance activities, we offer a free introductory call to help you assess risks, responsibilities, and the most proportionate route forward.
You do not need a fully defined programme to start the conversation. We offer a free, no‑obligation call to help you understand SOC 2 requirements, assess your current position, and identify practical next steps.

Blog, produced in collaboration with BSI, discusses the timeline for transition to ISO 27001:2022 and what you can expect from your transition assessment.

ISO 27001 is a standard for Information Security Management that provides any organisation with a framework to protect most valuable assets.

In this blog, we’ll take a look at management commitment, one of the most significant.



